NIST cloud reference model, Cloud types, services and deployment models, cloud APIs,
Cloud virtualisation, types of virtualisation from physical infrastructure
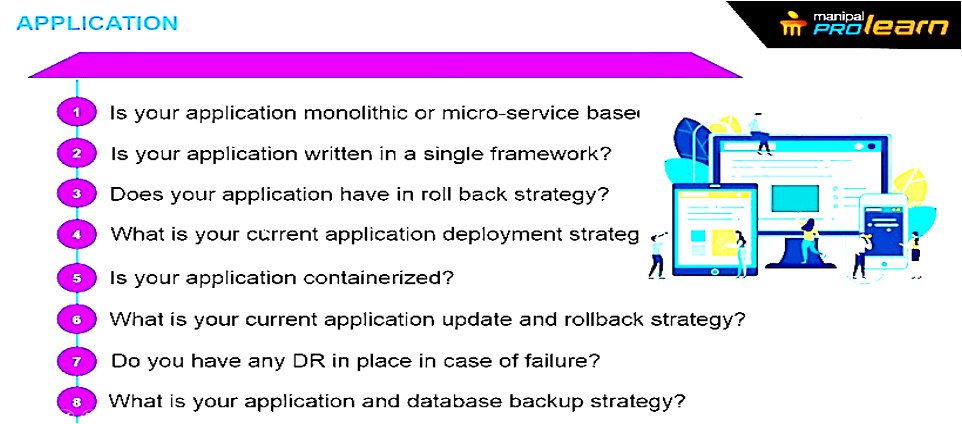
Pre-requisites:
- Hardware infrastructure
- Software infrastructure
- Operating system (Linux): We can deploy the packages manually. It is portable. It has high end security which is not possible with Microsoft. Most of the hardware
- Data centre facilities
- Virtualisation technologies
- Software engineering concepts: System development lifecycle. Information gathering, requirements analysis, design, loading and testing, debugging and deployment. Entity: cloud user, cloud service providers.
Networking concepts: What is OSI model? Why is it used. It’s primitive model of designing
IBM, oracle, HP
Ali baba, digital Ocean: medium size enterprises in Cloud computing
Email service: Don’t need PPO.
Companyname.com
Multiple websites can be put behind load balancer. If traffic is much.
PPU usage of average website goes above a certain limit.
Cloud computing is there so that one doesn’t have to pay additional for the services. It’s become very popular and more companies are using cloud computing.
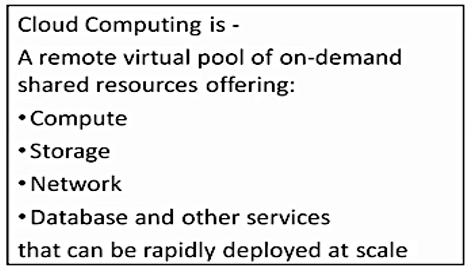
What’s cloud computing?
It’s remote, virtual pool. It’s used for solving the problems. What are the standard process for solving the problem. There are different types of methodologies like linear programming. Parallel approach the task is divided and then approached. Pipeline is type of parallel approach.
How to get from A to B if the distance is 10 km?
Divide and path rule.
Multi-model transportation system:
Offering
Database,
iCloud, gmail.
Netflix uses amazon’s storage service.
Scaling up means upgrading to higher RAM and higher CPU
Horizontal: adding more servers
Cost reductions: The price is very low. Capital expenditure is spent to operational .
Any organisation can switch to cloud computing and pay as you use.

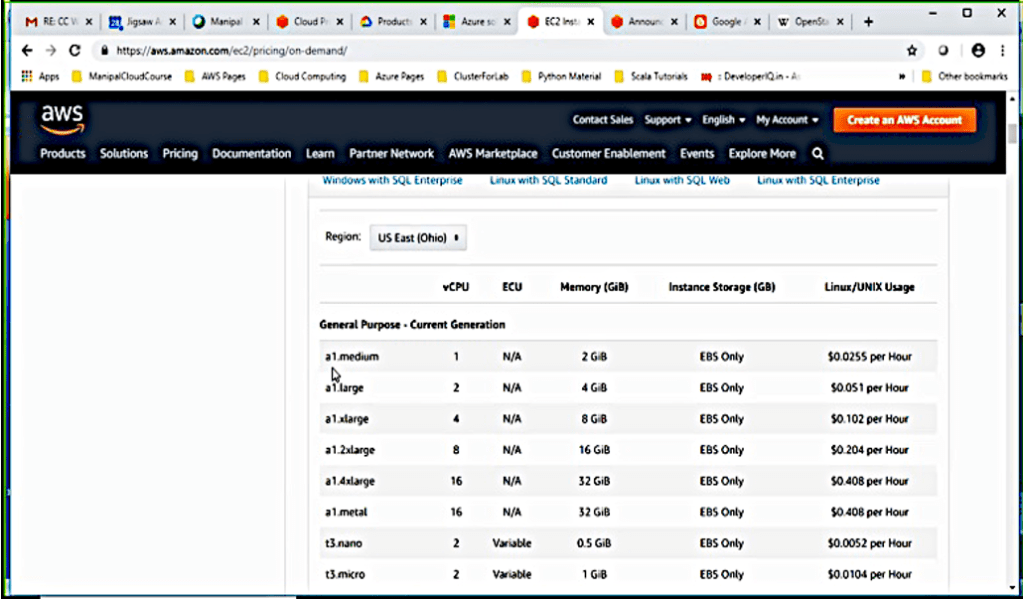
Charges for:
IP address, storage.
Prices are competitive. Reservation of IP address, no maintenance service.
If there are updates in SQL service, they will automatically take care. The update can be scheduled . The backup and replication will be created. If the data system goes down automatically the backup will take care, this type of maintenance is taken care of.
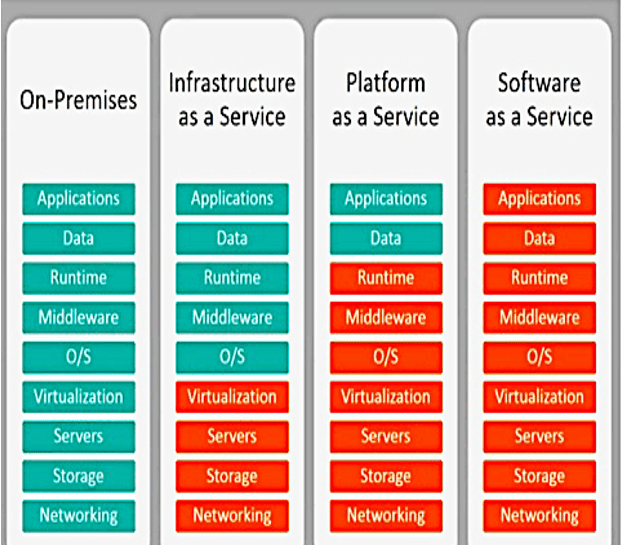
Platform as a service:
Data needs to take care. If one needs to deploy web platform.
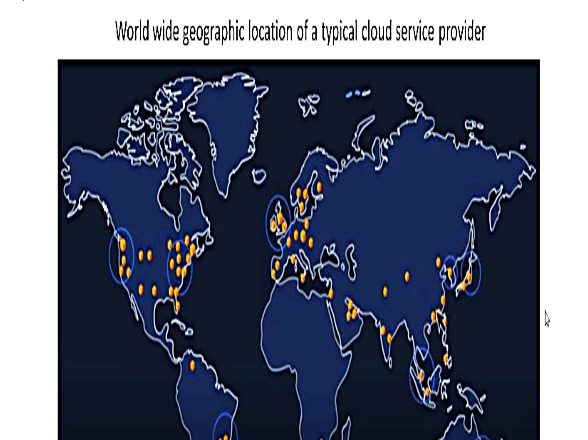
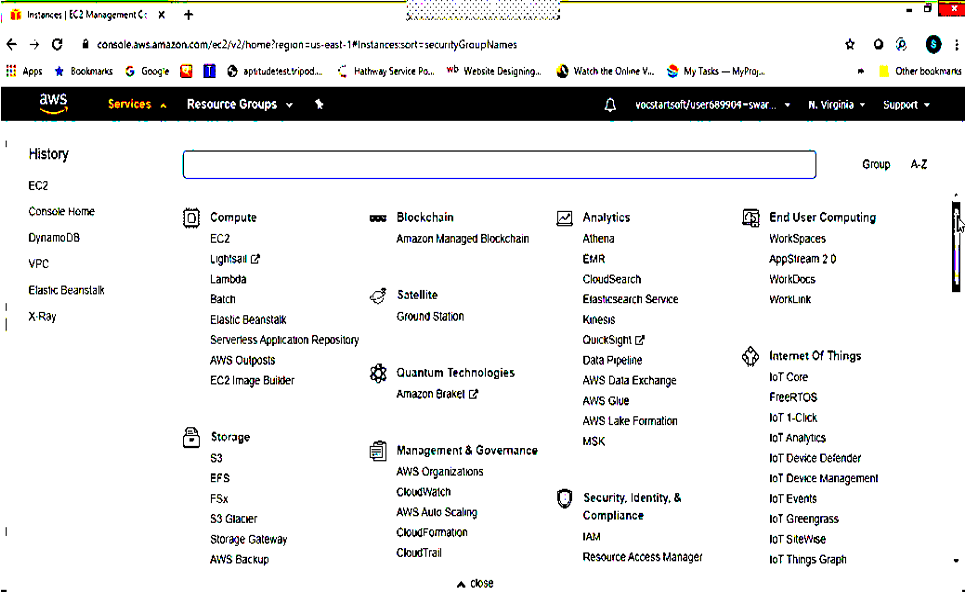
AWS Infrastructure:
Big data
Software as a service: SalesForce can record the interaction with the customers, Gmail, Microsoft365. We choose a provider, for uploading the website on the website application.
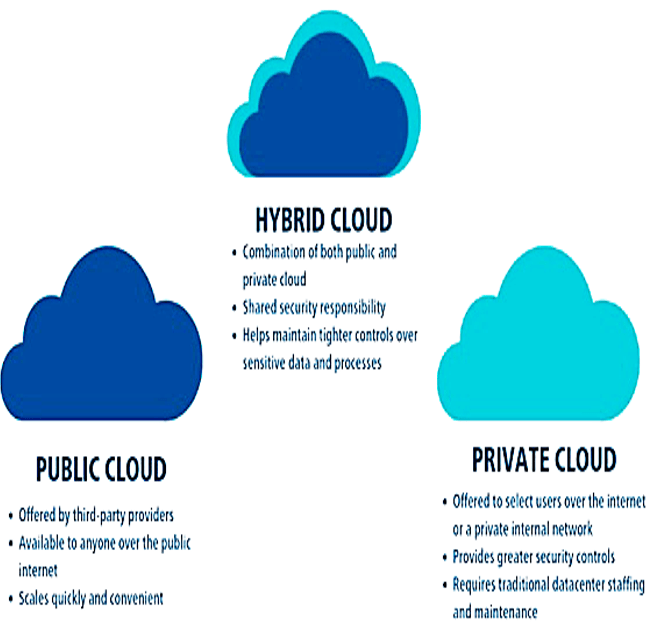
Cloud deployment model:
- Public cloud: Cost of service is low. It’s provided by cloud service providers.
- Private cloud: Cloud infrastructure exclusively for a single organisation. Storage, system and network. It can be located in premises or with the service provider like Amazon etc. It is exclusively meant for a particular organisation. It’s bit costly.
- Hybrid: Combination of public and private cloud. They can offer multiple deployment model for example if someone has sensitive data and an organisation would would like to build a business intelligent software. Data which is not can be sent over public. Organisation has a lot of services and there is a lot of traffic and there is cloud burst or temporary spike. The public cloud is taken an advantage of.
Amazon has its own RDMS.
Amazon Kinesis: capturing server logs and user behaviour
DNS is external server.
Auto scaling: When it’s peak time or maximum number of hits increase or when there’s degradation and there are less number of hits.
Docker provides multiple containers.
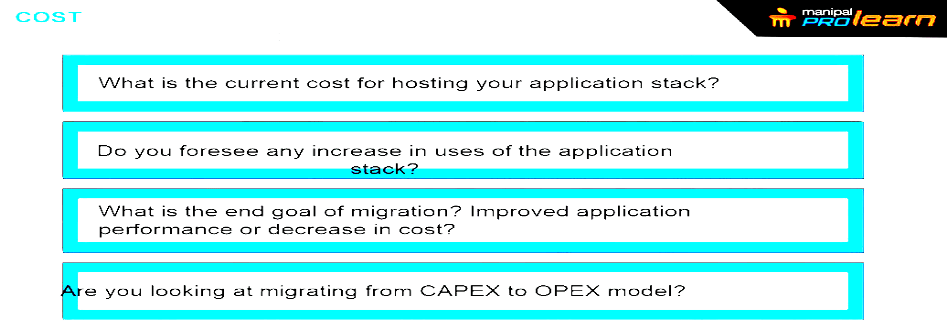
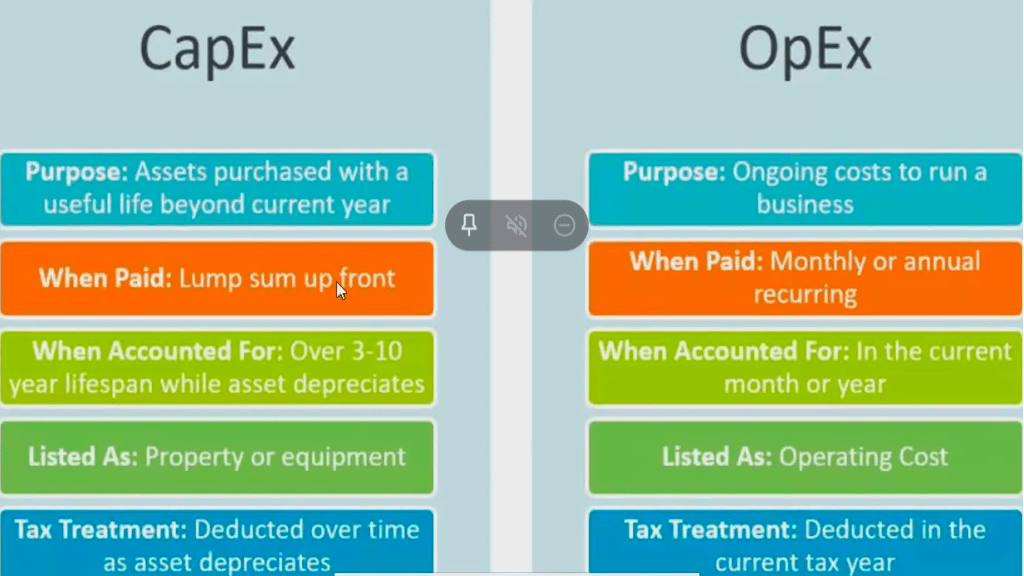
CAPEX: capital ex
OPEX: Operational Ex
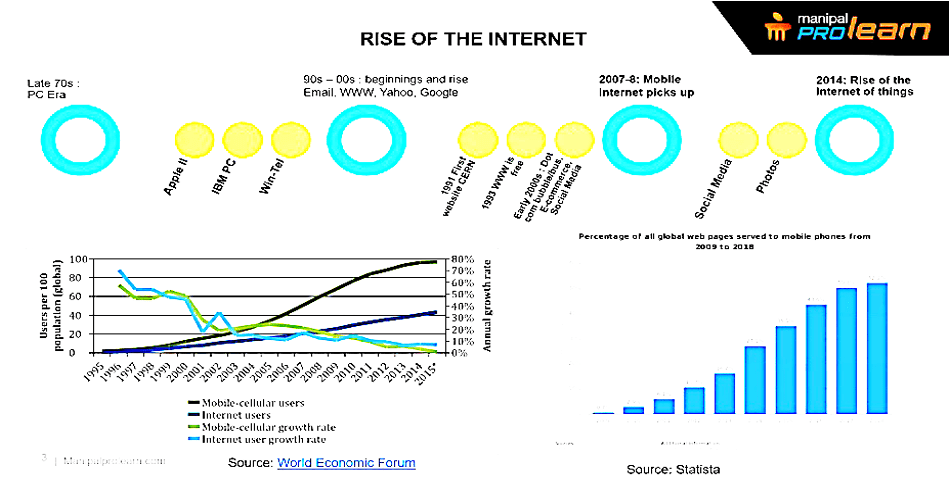
iPhone was designed to give full access to internet.
Primary use of smartphone:
Photos
Social media
Chatting and texting
Internet
Phone call
Mobile internet grew at the rate of 80%
Half of the traffic comes from mobile phones.
Internet anyway took decade to become mass popular
Mobile took 3-5 years
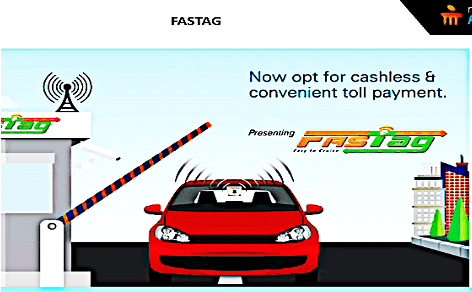
No longer wait for queues. This is about cloud usage to IoT. There is a receiver at the booth. There is an e wallet application. How does it works? It works on iOT and cloud plays a major role. It used RFID, NFC used in IoT tags. Does it have power? No. Booth’s NFC recover is connected to the back end which goes to the cloud. It authenticates if one’s wallet money has enough money.
It’s a fitness tracker for cows. It’s like fitness band for humans. What is the benefit? We can’t recommend fitness regime to cow. Based on statistics, the more active the cow is the more milk it is going to yield.

96 reading in a day. It downloads all the data to handheld. From there it sends to the doctor. The doctor is much aware about the blood glucose profile.
Washing machine connects to the internet. The company wants to know how the customer is using the machine. Videocon launched a fully automatically machine. Punjab and Haryana did not buy fully automatic machines. They send their marketing team door to door. Most didn’t buy the machine as they used the machine to churn the butter out of the milk. The machine is equipped with sensors. It checks the orientation of machine, weight of the clothes. Intelligent controller switches off and switches on the water and detergent intake. If something goes wrong with the machine it can notify the repair team itself.
Predictive maintenance: it starts giving some indication. Even the fan get too hot or rotate too fast before the motor burns out. Vibration and sound analysis of motor helps in predictive maintenance. It helps learn from past data of failure. All this is possible with IoT.
Ibaco iced creams: 20-25% inventory loss due to power outage.
Simple IoT implementation by nimble wireless. It can regulate the temperature to some time. Automatic phone call. If the CEO is having a meeting with the operation, marketing and finance team.
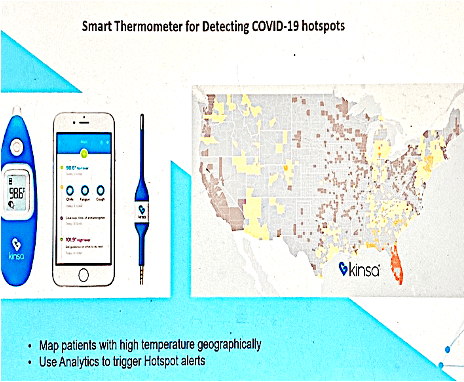
Rolls Royce engines: Checked turbine speed, coolant pressure. All the data is sent to centralised data centres.
Navigating unprecedented challenges with cloud
Remote work is working smarter with IBM cloud. The customers get answer faster with Watson assistance from hours to minutes. It helps rethinking how business moves forward.
IBM has been already been embraced by businesses to tackle challenges and be more responsive. Cloud based solutions are helping systems run smoothly, remotely and securely. This is critical since 75% of the work force is working from home. The need to engage customer digitally is stronger than before. New problem need the new thinking I’m confident and it’s fine to be part of the solution to the challenges of the future ready world. As we reflect this year challenging in many ways it is also a catalyst in human reflection and human adoption through acceleration to the acceptance and advancement of remote working and remotely learning. Running on a secure cloud which is also in this crisis has proven that hybrid cloud is as we are smarter and more resilient through COVID-19. Business in governance that were in path of multiple years are being condensed into less than a year and even months. Value is being derived from modernised apps running on secure cloud which is also enabling AI. Crisis has proven that beyond a point a doubt hybrid cloud is a underpinning platform that redefined business in eco system as we emerge smarter and resilient through COVID-19.
Collaboration and trustable partnership can be used to solve problems , overcome challenges and rethink how work can be refined and services be provided. The university of Queensland in Australia leveraged IBM Watson AI, IBM cloud and security to redesign cloud web application to help clinical researchers act and securely share data for COVID19 treatment.
The Indian council of medical research, ministry of Heath, community welfare and government of India have collaborated with IBM research lab to deploy a virtual agent and assistance to boast rapid response to India front line testing ability. This virtual AI is able to comprehend and response to authorised queries across India in both English and Hindi. The ministry of digital economy in Thailand collaborated with IBM for solution to working from home further efficiency and provide digital services through lockdown that are now new standard for easing stand and recovery. Since this crisis started, we saw common tactical challenges across multiple industries in countries. Making supply chain more resilient to resist to global shock, moving the right work load to the cloud to have critical functions up and running while quickly deploying services by automating right IT task for the workforce, securing ITBM structure to enable remote working and using AI to handle the massive increase in calls and request.
Organisation who are optimising the cash flow through accelerated agendas, examining process rip flows and finding opportunities to implement automation, AI and collaboration tools and reimagining services in the cloud so there can be urgent need and demand for efficiency and speed. Using which cloud partner and which cloud form powering the business are very consequential decisions.
Cloud strategy to introduce flexibility, security and openness. Open architecture enables one to build once and run any-where.
A hybrid cloud strategy that includes moving mission critical workloads to the cloud even in regulated businesses like banking.
Watson works: AI models to deliver data driven insights to COVID related work place challenge from space allocation to contact tracing, even mass detection and for data privacy and ethics
Watson AI provides complete and accurate view into the IT incidence and gives timely insights to give complex issues quickly to minimise service disruptions.
Edge computing solutions for the 5G era leveraging Red Hat.
IBM cloud satellite which enables IBM services anywhere.
The public cloud is rearchitected using red hat open shift container platform built on Kubernetes and delivered accords 60 global data centres. IBM cloud and red hat have brought together market leading security, enterprise scalability and open innovation for increased agility and business continuity.
The clients are being helped by running virtual garages to help them with their cloud strategy and speeding application modernisation and addressing urgent cloud native development needs. For highly automated cloud services the cloud management services are being managed.
Helping clients balance cost pressures through financial transparency of multi cloud management.
Cloud can help in innovate, transform and excel at your business.
The computing era started improving with the following things:
Hardware architecture : Design OS soi it can cover all the existing error and improves the performance.
System software :
Packet transmission from the gateway.
Problem solving envrionment : Team building,
Network tracking analysis : Power analysis.
The components of computing eras are going through the following :
Research and development
Commodity
Motivation related to Cloud computing :
Core in an processor : 2,4,6,8,10
Super computer :
Fugaku-Fujitsu
Summit-IBM
Sierra-IBM
Sunway TaihuLight
Tainhe-2A
Indian
Pratysuh -Cray Inc
Mihir- Cray Inc National centre for medium range weather.
Enery efficient super computer green
MN3
Selelns-N
PARAM is the 1st supercomputer in India. It is designed and assembled but the Centre fot Development of Advanced Computing (C-DAC) in Pune, India.
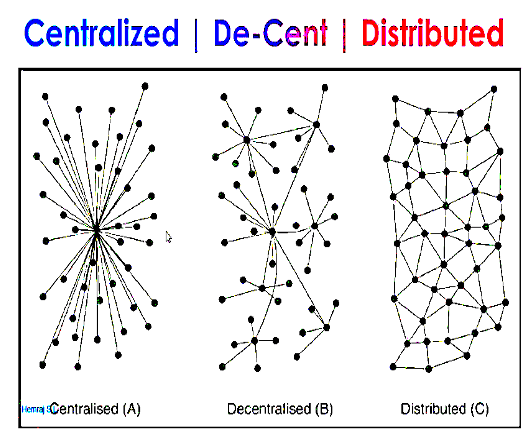
All the systems in infrastructure are centralized. The limitations are Gateway to ISP to the external world.
Authentication protocol: whenever a client wants to access a server, server will again authenticate if the client is authentic or not then revert back to the client.
If a user is not registers, it asks them to register. This system is more secure.
Library system: All the libraries are connected to the central libraries. Quora, medium, etc. Real time example of centralized system: The server in state of bottleneck. It won’t respond the requirements of the client.
Decentralised System:
- Cryptosystem uses this. Example: Google.
- Latency increase: Amount of time taken for server
- Characteristics: As an entire system.
- .
- Distributed Computer System:
- Closely looped. Independent process.
- Latency: Network delay before any data is sent.
- Process of dividing a program into large tasks. Large number of computation takes place. This causes load imbalance. Few tasks process the data while some part sit idle. Granularity is parallel computing.
- Reliability
- Fault tolerate: Can tolerate if there’s system failure.
- Security: there are policies to deal with threats to the communications or processing of data in a system.
Grid computing:
Computational
network
Utility
Collaborative grid
Data grid
IRCTC has 5 servers in zig zag format.
Bangalore, Delhi, Hyderabad, Kolkata, Mumbai.
NIST: National institute of science and technology.
Definitions:
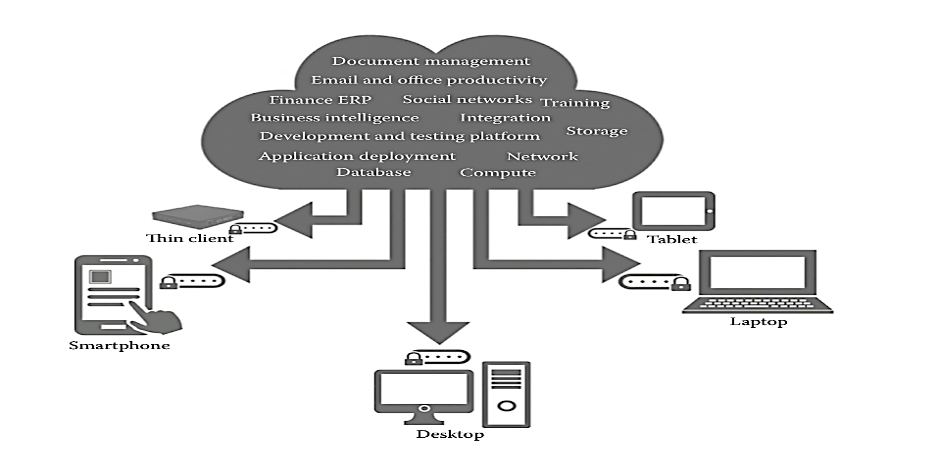
According to NIST, Cloud computing is a model for enabling convenient, on demand network access to a shared pool of configuration computing resources (networks, servers, storage, applications and servers). The cloud model promotes availability and is composed of five essential characteristics three service models and 4 deployment models.
Or
A cloud is a type of parallel and distributed system consisting of a collection of interconnected and virtualized computers.
Any software has:
- Packages
- IDE
Everything is integrated to the web browser. This reduces data space and complexibility. The user needs services only.
Properties of cloud computing:
- Scalability: Dynamic provision, multi-tenant design.
- Availability/reliability: Fault tolerance, system security, system resilience
- Manageability/interoperability: Control automation, system monitoring, billing system
- Accessibility/portability: Can use on any equipment.
- Performance optimisation: Job scheduling, load balancing, parallel computing.
- Job scheduling: If printer comes under services, all the users request the printer to print same document at same time. It enables to check which user requested first.
The different types of processing:
- FCFS: First come, first serve. This algorithm is used by cloud computing.
- SJF: Shortage Job First: If user 2 has requested to print 2, user 3 has for 10 pages, user 5 for 5 pages. It finds out which will be the least one and put it first.
- Round robin algorithm:
- Priority scheduling:
Enabling techniques: hardware virtualization, utility and grid computing, web services, autonomic computing
Autonomic computing: There is a commercial software from solar. Data system software management. It helps manage the load automatically. If there is no load it shuts down automatically.
Cloud computing focuses on virtualization it helps in improving resource utilization rate. It utilises the under-utilised resources. Data centre can handle load of 1 billion users. But the service is used by only 10 M use. Only 90% is used. So it donated to other cloud computing. After a month the load increases to 990 M users. 0.1% is yet not utilized.
Two essential concepts of Cloud:
- Abstraction:
- Virtualization:
- Pooling and sharing resources
Outsources system administration
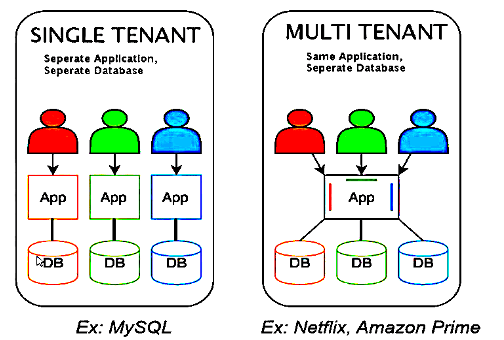
| Single Tenant | Multi-tenant |
| Used for big organisations | IRCTC, Google meet |
| Involves marketing, sales, finance, HR, accounting, etc. | After the user has registered, they get a separate database |
| Different tenants for different purpose. | The app acts as an interface between the users and the organization. |
| Dependant and more customised. | Affordable cost |
| Multiple customers to share the same applications pr the same physical infrastructure while retaining privacy and security over their information. |
With cloud computing:
Location independent
Rapid scalability
Self-service
Standardized service
Automated service management
Virtualized resources
Needs internet
Logical resources is mapped to physical resources.
69% of enterprise organisations are currently migrating data for enterprise resource planning (ERP) applications to the cloud.
Why do enterprise migrate to the cloud?
- No money needed for infrastructure.
- Speed and cost saving.
Need advantages such as disaster recovery .
Python is an interpreted language which executes line by line that’s why it s
Private clouds: E-mail.
Top level:
On-premises data: own resources and own infrastructure. HP, VMare, IBM
15th September
Bare metal v/s virtual resources
Bare metal means on premises.
Benefit
How is data retrieved from the source to the destination
Laptop > Router > DNS >ISP > Internet > ISR(R) > DNS >
Router
Optical fibre reduces time, ethernet increases time.
HyperViser or Virtual Machine Monitor (VMM)
It is a computer software that creates or runs virtual machines.
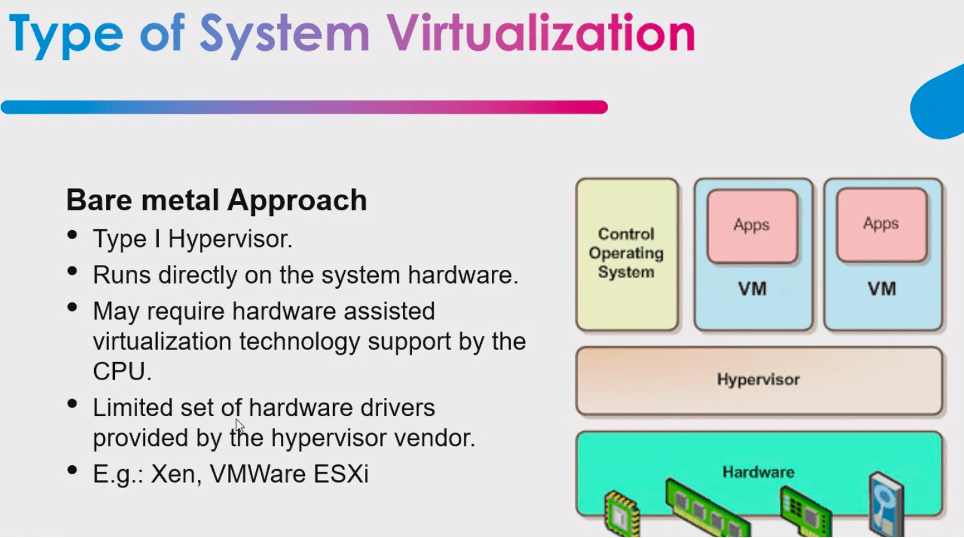
Type 2 is also known as hosted. HyperV, VirtualBox
Type 1
Type 2 virtualization
Economics
Economics is the study of what constitutes balanced human behaviour in attempt to fulfil the needs.
It has been a powerful force in driving industry transformations and as more and more customers evaluate cloud computing investments that will significantly affect Return of Investment.
Deal with the productions, distribution, and consumption og IT services.
Scope not limited to Cloud Computing paradigm’s Financial benefits.
It is more about choices cloud customers make
To inquire and why?
Economics of Cloud should show the way and show not confuse not the adopters. It is important for cloud computers users should know their exact needs. The decision makers in an organization is stake holders.
Resources utilization: capacity
Opportunity cost= Return on the best option which is not chosen.
(Invested X dollars in Y company/return on the option)
Suppose after 1 year:
AWS: 5% interest
GCP: 10% interest
O.C.=(10-5)%=5%
Estimates vary widely on possible cost savings
“If you move your data centre to a cloud provider, it will cost a 10th of the cost.”-Brian
To run a successful business:
CapEx: When business acquires assists that could be beneficial. Service provider, licensing of a software, trademark
OpEx: Business incurs to run smoothly every single day.
IRR
NPV
Total cost of ownership
Cloud migration
Cloud migration is the process of relocating an organisation’s data, applications and workloads to a cloud infrastructure. You organisation may choose to relocate all its computing access to a cloud, however, in most cases, some application and services still remain on premise.
When data is very huge what all steps can we do? We can directly store the data on to the cloud because when we move from the on premise infrastructure to on cloud infrastructure.
Why should to 1 consider cloud migration?
Less use of physical hardware resources. If you don’t have any hard words infrastructure or resources or time and money to maintain the internal servers and operating and managing the servers in such case we can directly choose the cloud infrastructure to benefit the customers.
According to Bloomberg and got now reported that at the end of 2020 more than 80% of enterprises date will pass through the cloud. Every organization is moving towards the cloud so the huge data can be stored on the cloud resources.
It would be better to learn swimming then to sink. So the organisation should switch to cloud to provide high efficiency to the customers.
Ego governance was initiated by the government of India from 2014 onwards. Most of the government facilities are moving to the cloud. For making a particular certificate first the people had to go to the collector office manually but now this customer support Centre to fill online form and upload the documents which supported the application. This certificate is generated on the go.
Why do we need migration from on from mice to cloud environment
- Your application is experiencing increased traffic and it’s becoming difficult to skilled resources on the fly to meet the increasing demand. Before 2010, IRCTC they had five huge servers which was exact around India only which were located in Kolkata, Mumbai, Hyderabad Bangalore and Delhi. That time the uses of IRCTC user is a very less but since it adopted clout that LG since 2010 onwards the overall load shifted to the cloud. We can also take the examples of Flipkart big billion day sale.
- To reduce operational cost while increasing defectiveness of IT processes.
- Your clients require fast application implementation and deployment and thus want to focus more on development while reducing infrastructure overhead.
- Setting multi region infrastructure is tedious to expand the business to graphically is challenging. We can provide service to any geographical location. Storage is cheaper in cloud rather than in the hardware. They also provide free tier.
- Expensive storage.
Benefits of cloud migration:
- To build a widely distributed development team (loves loves to work remotely via Internet bracket close.
- To establish disaster recovery system, (cloud allow better recovery system at much better control over resources). Cloud provides entire copy of the virtual machines, which includes CPU and hard disk including to operating system. It takes a snapshot or makes a copy of the entire virtual machine. Virtual machine can struggle, the cloud automatically runs to be a machine. From old virtual machine to new virtual machine.
- Tracking and upgrading underlying server software is a time consuming. Clout provide automatic updates and handles many administration tasks such as database backup, software upgrades and periodic maintenance.
- Capex to Opex: cloud computing shifts to pay-as-you-go model, which is an attractive benefit, specially for start-up.
- On from my service usually have long development time. Whereas you can deploy the cloud in few minutes for relatively little cost.
- There are significant upfront capital expenses associated with Home from mice, there are few upfront expenses to the cloud.
- You need an internal or external security expert who is following the latest I will security threat and can develop a plan to protect your organization for on from my service. The risk of breach is to create for anyone, but a provider will invest heavily in security.
- Maintenance is extremely high on premise, whereas CSP does programmer in security updates automatically.
- It is very difficult to scale on from my service, cloud a scalable (up and down) on the go. Scaling can be horizontal scaling or vertical scaling.
Steps of calculating migration cost:
Gather all assets specifications, performance data and details of all running process, including software, servers, storage, security, networking infrastructure, and data.
Determine direct cost (include purchasing resources) and indirect costs (Will be relating to downtown,
How to migrate on premise to cloud?
Moving data to the cloud, moving data to the cloud is one of the most important steps of any migration. Cloud providers charge fees for transferring data to the systems.
Integration and testing of apps. Unfortunately, some applications just aren’t ready for the cloud. Example: ERP software and legacy software.
Consultant fees: a cloud migration can be difficult, and you may need outside expertise and experience to assist.
Migrating existing applications to the cloud involves three steps:
Before migration or pre-migration:
During migration: Entire application is run to the cloud server.
Post-migration: try configuring the software to make the application run smoothly.
There are four kind of deployment models:
Public
Private
Hybrid
Goal 2: I have made enough investment for on-premise storage, how can I get best of Cloud alongside?
Hybrid. It’s helping integrating other cloud services. It’s an integration of public and private.
During migration state:
Before for the moving to how of the cloud migration process, heroes formula suggested by AWS to determine how much data can be transferred and how fast.
Number of days is equal two: total bytes/(megabytes per second into network utilisation cross required time)
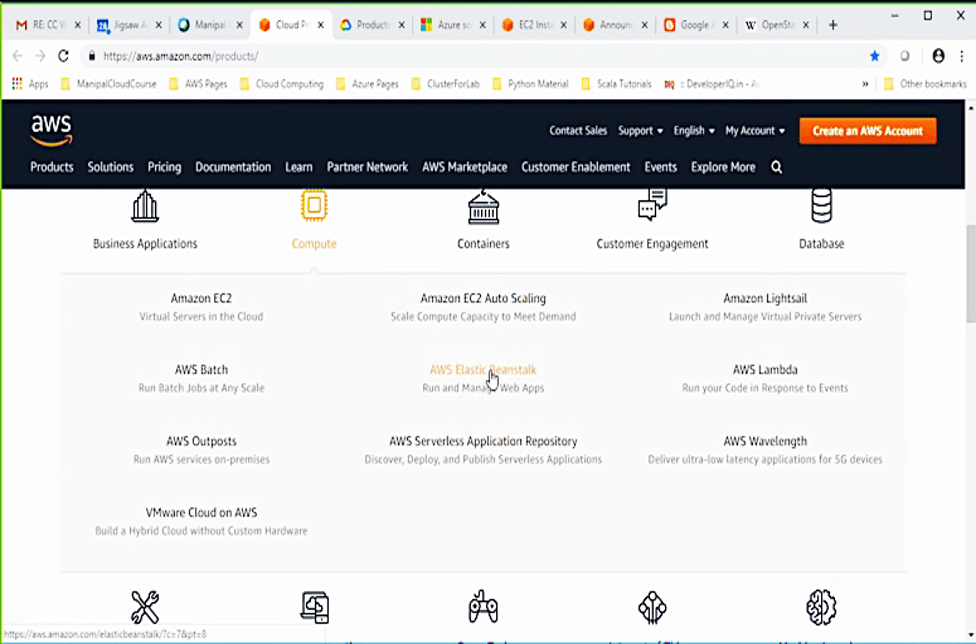
Top five most used a WS product
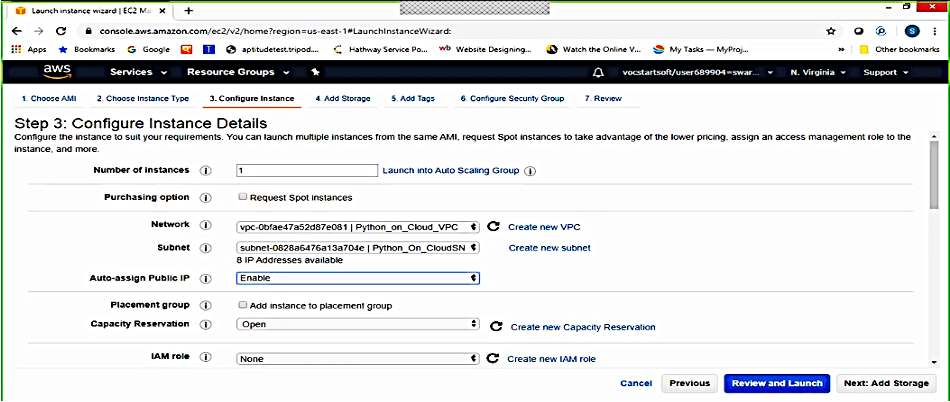
Compute: Amazon AC II, elastic container service, EWS patch, lambda, VM Ware clout AWS, EC to autoscaling, etc.
Storage: Amazon simple storage service (S3), FSX for L Leicester, AWS back up, Amazon elastics Lok store (EPS) etc. 89%
Database 79%
Five steps for cloud migration:
- Planning and assessment
- Migration tools: There are online migration tools and off-line migration tools.
- Cloud storage options
- Migration strategies
- Application migration options
Planning and assessments
The plan and assessment face is divided into:
- Financial assessment: Deserve a cost to maintain all the cost. To maintain the higher scores over cost this track interest structure, PDUS2 are switches and maintenance, software, virtualisation license
- Security and compliance assessment
- Technical and functional assessment
Security and compliance assessment:
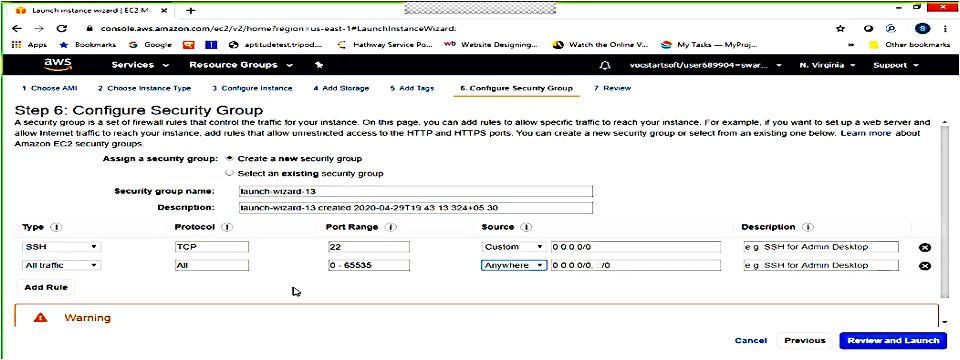
It is important to involve security advisors and auditors early in this process. Since status security is a challenging task in crowd migration.
- Overall risk tolerance
- Main concerns around availability, durability, and a confidentiality f your data.
C: confidentiality
I: integration
A: availability
Technical and functional assessment:
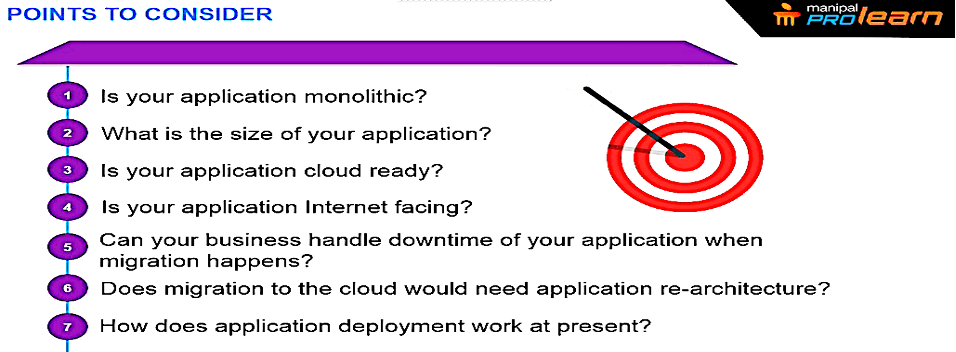
It is important to understand what applications are suitable to the cloud strategically and architecture only. This will help you decide:
Questions you should ask yourself before moving into the cloud:
Which application/data to move into the cloud first?
Which data to transfer later?
Which applications should remain in house?
Migration tools:
There are physical limitations when it comes to migrating data from on from my sis locations into the cloud. That’s why migration tools come to the rescue. The migration tools helps you to move data to Road, networks and technology partners.
If you need easy, one and done method to transfer data at small scales, go to the following tools:
Pleasure command line interface – on premise data and it is highly secured.
S3 command line interface – write commands where the commands can be written directly into the S3 bucket.
Rsync command: it is an open source tool combined with third-party file system tools.
Ghost Sync: used to import the data of NSA.
Cloud storage options: AWS
Direct connect
Snowball
Storage gateway
AWS cloud migration tools:
| Ideal for | Data migration tool to be used | |
| Migrate petabytes of data in batches to the cloud | AWS import/export snowball | |
| Migrate exabytes of debt and batches to the clou | AWS snowmobile | |
| Connect directly into AWS regional data centre | AWS direct connect | |
Various storage option available with AWS cloud
| Static content distribution read – many types of objects storing large right ones | Non-persistent transient updates | ||
Migration strategies:
There are two strategies that will help you move part of your entire system to the cloud without disrupting the current business.
- Forklift migration strategy
Self-contained applications, tightly coupled applications, or stateless applications might be better served by this approach. In state full application the request always depends upon the server. The best example related to state full is login application credentials. What is the user clicks login the data will be forwarded to the particular server. The server will check the data, if the credentials are available in the database then only it will create a session for the user for a limited amount of time. For limited amount of time the user can access the server easily. When it comes to stateless application, the user does not have to depend upon the server for processing. The best example is search engines. Some query is processed into the search bar. If the server doesn’t load the particular pages, the query is run again. There are no sessions in stateless applications everything needs to be managed dynamically.
- Hybrid migration strategy:
Considering some parts of an application and moving them to the cloud while leaving other parts of the application in place. I will for large systems involving several applications.
Application migration
- Life migration: the process of moving a running application from physical machine to cloud infrastructure without disconnecting the application. Example: memory, network connectivity, and net storage of the virtual machine are replicated from the physical device to the cloud.
- Host cloning: cloning the operating system image and typically one-time migration.
- Data migration: synchronising the data between computer storage to the cloud.
- App containerisation: SOS level virtualisation method for deploying and running distributor applications.
- VM conversion: converts virtual machine disk (VMDK) into cloud recognisable format. The traitor is transferred via API.
Post migration stage
- Leveraging the cloud
After migrating your application, don’t forget to run the necessary tests, and confirm everything is in place. Invest time and resources to explore the additional benefits to the cloud. You must:
Leverage into price support
Leverage other services like autoscaling service and elastic map reduce
- Monitor and optimise
Understand, monitor, examine, observe
- Use cloud monitoring tools:
It uses automated and manual tools to manage, monitoring and evaluating cloud computing architecture, infrastructure, and services.
Some tools are:
- Amazon cloud watch
- App dynamics
- Microsoft cloud monitoring
- 1
- Hi Prakhar
- Solar winds
- X a price
- Retrace
- PagerDuty
Transfer data to EWS (how much it cost):
AWS virtual private network
AWS virtual private network (EWS VPN) allows users to establish a secure, private connection from the network a device to the AWS cloud. There are two options when it comes to using EWS VPN:
AWS side to side VPN connect you on from ices network or a private IT infrastructure to the cloud
AWS client VPN connect users to EWS or on premises networks.
AWS VPN is in cryptic, quick to and pretty cost effective for small data transfers. It is a shared connection, however, so it’s not always as reliable as other options.
AWS data sync
AWS data Singh is a service that allows users to automate the shifting of data between on premises storage and Amazon S3 or Amazon EFS.
With
EWS novel:
AW a snowball can store data up to 80 TB.
Potential risk of cloud migration:
- Consumers have reduced visibility and control
- On demand self service simplifies unauthorised use
- Internet accessible management Apis can be compromised
- Separation among multiple tenants fails
- Data deletion is incomplete
- Credentials are stolen (improper use of privileges open)
- When the lock in complicates moving to other CSPs (cloud service provider)
- Increase complexity strains IT staff
- Insiders authorized access
- Stored data is lost
- CSP supply chain is compromised
- Insufficient due diligence increases cyber security risk
- The end user does not have complete autonomy while running cloud applications.
- Unauthorized access to William instances.
- Shared cloud services exploits.
- Secure release on issues
Migrating risk:
- Ensure that users have appropriate privileges
- Automate processes, like database backups.
- Identify potentially malicious users.
- Analyse and monitor CSPs.
Example of MapReduce:
Big data is split into clunks.
In the first phase the source code:
- Lexical analysis
- Syntax analysis
- Semantic analysis
Case: cost benefit analysis of coal cloud computing in education
Challenges associated to education system in universities and colleges:
- Purchase of costly hardware
- Maintenance and updating of hardware
- Installation of hardware
- Decreasing lifespan of software
- Hardware
- Purchase of costly licensed software
- Purchase of newer versions software
- Purchase of antivirus programs
- Purchase of operating systems and applications
Challenges associated to students in IT departments
Limited time period and non-availability of the resources
Portability and compatibility of existing hardware
Portability and compatibility of newer software
Computing power and resources
Limited bandwidth utilisation
Delay in purchase.
Cost and leases of on premises versus cloud and education
Requirement analysis
Institute in Pune wants to set up a new lab fourth student with following requirement of:
20 computers of Intel I five processor with Windows 10 OS
To server of IBM 64 (Sion-based, primary and secondary) having capacity of 10 TV
Software: license windows OS, SQL Server,.net, MS office.
Wi-Fi controller – 25 units
Invoice of five TB
UPS of 20 kVA
Switches, hubs, how to use etc (Cisco)
Band with least line internet – two-way
Private email server
Exercise:
- Perform a comparative cost benefit analysis of all premises IT infrastructure and cloud-based services for SCIT
- Estimate configuration and implementation cost.
- Estimate recurring cost (up to 3 years)
- Calculate termination cost.
- Calculate TCO (for on premises and cloud)
Migration testing: Migration testing allowed to move data from the legacy system to the new system without any data loss and there are several types of migration testing:
- Application migration: in application migration it is a process where entire application is migrated from one environment to another platform. Some benefits are:
- Reduces operational and maintenance costs
- Reduces dependencies on other systems.
- Eliminates or migrates risk in business. Enhances the performance of the system
- Enhances technical support and administration.
- Support additional features and bug fixes (if any)
Database migration: DBMS is converted to our DBMS. It is the type of migration with the data in the database of an application is migrated to another database.
Some benefits are:
- Application can have multiple databases at the backend to support huge customer data.
- Data enhancements can be achieved.
- Proper analysis of data will help in improving the data quality.
- Data sampling and data cleaning helps in keeping the database clean.
- To carry out data analytic
Server migration:
Server migration is a type of migration with the server details move from one server to another server. Your configuration also gets migrated to the new server along with the server data.
- OS migration: Who is migration is a type of migration where an application is migrated from one operating system to another. This involves a lot of challenges and huge risk of compatibility. Even network, confrontations, interfaces, and a lot of component required the redesigning. Some benefits are:
- Increase virtualization where migrated to a cloud-based platform
- Lower cost and operations And maintenance
- Increase speed, support, productivity and security.
Testing consideration and focus area:
Application changes and on premise interfaces
- Data migration
- Security: The data needs to be secured by encryption..
- Performance
- Scalability: not possible on premises.
- Availability and disaster recovery
- Incident response on cyber attacks.
Cloud security
2013: hacked Yahoo‘s 3000,000,0 email accounts gaining access to sensitive customer information.
2013: use small way to steal data from target company point of sale system is compromised information of approximately 110 million credit/debit carrying customers.
2013: Edward Snowden (CIA employee on contract) breached NSE database. The process of exfiltration is to get off the network.
Once an attacker gets access to the system he will delete all the locks, foot prints he will make changes to the machine configuration. The good hacker will always try to delete the things which will leave behind the footprints. Ghostsync, Rsync utilises the bandwidth.
2014: Syrian electronic army cyber hacking group inflated eBay‘s network stealing sensitive information of 14 5 million users.
2015: hackers broke into Antima included servers and store 37,.5 million records consisting of sensitive information.
2016: Russian-based cyber attackers hacked MySpace compromising over three 360 million account.
2016: Uber reported that hackers stole the information of over 57 million riders and drivers.
2017: cyber attackers hacked into Equifax servers and exposed over one 43 million customers personal information.
2017: 41 2 million user accounts were stolen from friend Finder sites.
2017: 147.9 million customers affected by the Equifax preach.
2018: cyber attackers hacked into merit international and compromise 500 million accounts.
2018: Facebook code was exploited by attackers and 50 million users account compromise.
2018: “I was hacked information belong 200 million users compromise. 2018: under armour reported that it’s my fitness pal.
2020: do you hotels in Marie disclose the security breach that impacted the debt of more than 5.2 million hotel guess who is the companies loyalty application..
2020: MGM resorts suffered a massive data breach resulting in the leak of one 42 million personal details of the hotel guests.
2020:5,00,00 stolen zoom password available for sale and talk with crime forums.
2020: University of California – SF database act (1.14 crypto currency in BTC)
2020: medical and health was struck by a Ransom where attack and data we started that 365, 000 patients are affected in the sophisticated cyber attack.
2020: Twitter breach well coordinated scam made attackers swindle dollar 121, 000 in bitcoin Through nearly 300 transactions.
According to Gartner the worldwide information security market is forecast to reach dollar 170 .4 billion in 2022. It will reach to dollar 1 trillion in 2025.
Critical component of information security:
Data at rest: Data in the hard drive
Data in use:
SaaS
Points backed with stats.
Bare metal server/live server: server connected through internet
App services: URL will be generated which will help access webpage using internet
Container services
Internet
Introduction
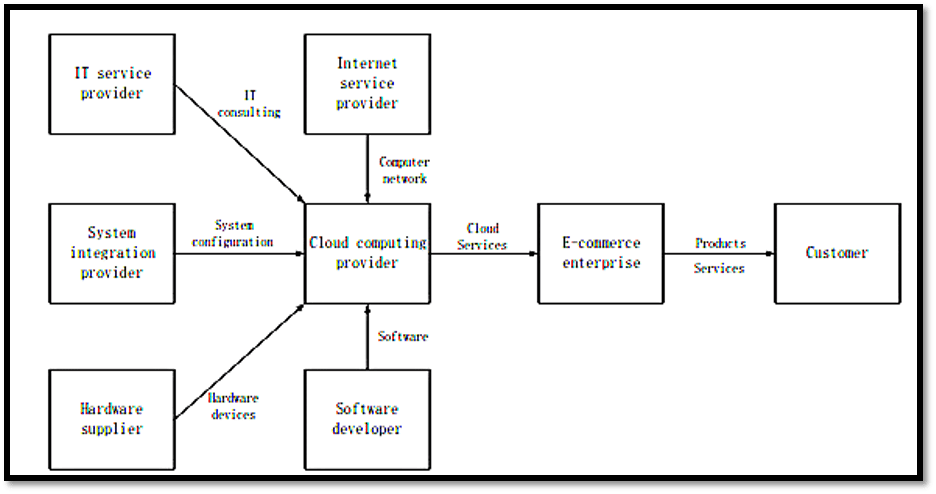
E-commerce has grown phenomenally in the last decade, with its growth the data produced has also increased creating the hurdle for the e-commerce industry to properly manage, store and use the data for future use. Here cloud computing comes into play, it provides the e-commerce industry with the scalable resources to deal with all the difficulties related to data.
All the companies started adapting cloud computing to move their applications to the cloud. It is a remote and virtual pool of resources useful for solving problems. Virtualisation helps companies save on space, energy,
and personnel’s. On-cloud, people have facilities not available on-premises. Cloud is available to the business on their demand, as much required and at pay as use price heightening its popularity.
The growth of e-commerce and internet can increase the traffic flow on the site leading to downtime, system outages and data loss causing inconvenience in business. It is very important for online business sites to handle such situations, IT infrastructure and its cloudification plays a crucial role here. Cloud provides with scalability, availability and flexibility, unlike the traditional hosting services. Downtime of websites can be eliminated by using multiple server zones offered by a good quality provider.
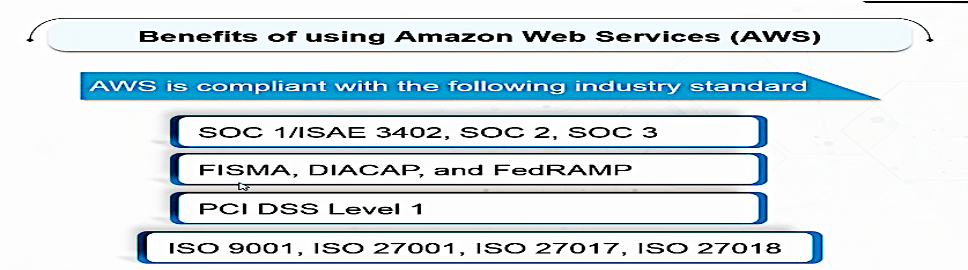
The main concern of business about transferring the data in the cloud was of security which was solved by introducing strong authentication tools, levels of authorisation, data protection regulations, etc. Over the years many new cloud providers in the market like Amazon web services (AWS), Microsoft Azure, IBM SmartCloud etc benefiting the industry by providing great services with security.
Cloud computing
The new computing era has started a revolution in hardware and software by providing a problem solving environment.
As stated by NIST, Cloud computing is a model for enabling convenient ,on-demand, network access to a shared pool of configurable computing resources. Cloud computing is the on-demand delivery of IT resources and requirements via the internet with pay as you go pricing. Instead of investing in the data centres and servers, one can access technology and computing services provided by cloud for storage, developing and managing the data on an as-needed basis from a cloud provider
Many companies and industries are moving towards adopting cloud computing. There are four cloud clement models:
- On-premises.
- Infrastructure as a service.
- Software as a service.
- Platform as a service.
There are three type of clouds:
- Public cloud
- Private cloud
- Hybrid cloud
Private cloud is best known for security controls. It requires traditional data centre staffing and maintenance.
AWS has a strong leadership compared to other competitors.
Azure provides huge discounts for existing Microsoft users. It is the fastest growing cloud provider in the market. The software updates for the servers are automated. It has predefined machine learning models and built in support for SQL workbench.
There is flexibility to migrate existing Microsoft based from on premises to Azure.
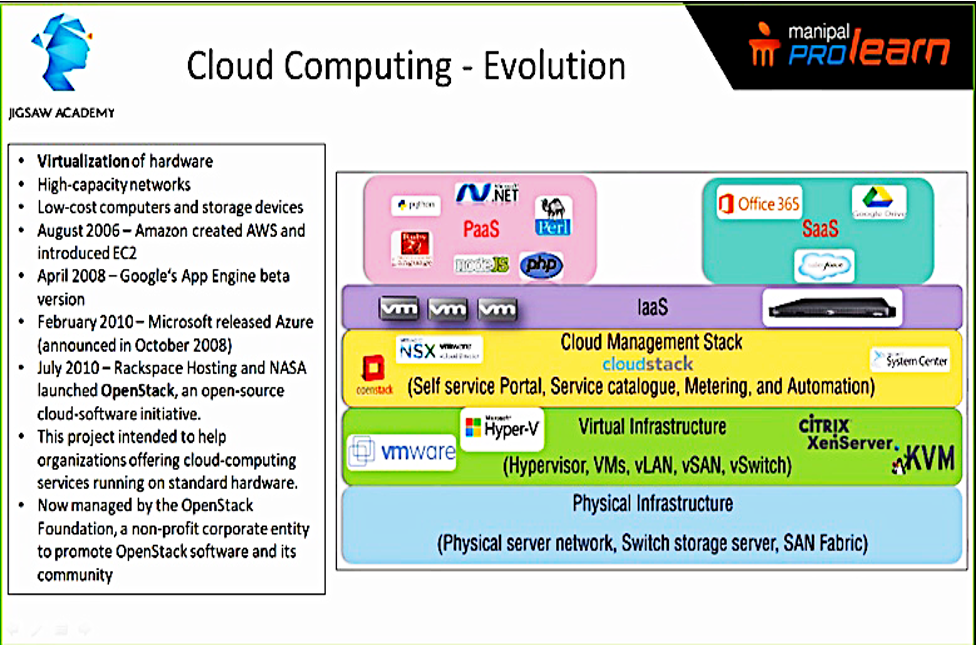
1.1. Evolution of Cloud computing
- In April 2006- Amazon created AWS and introduced EC2.
- In April 2008 – Google’s app beta version.
- February 2010 – Microsoft released as Azure (announced in October 2008)
- July 2010 – Rack-space hosting and NASA launched OpenStack, an open source cloud software initiative. This project intended to help the organisations offering cloud computing services running on standard hardware. It is now managed by the OpenStack foundation, a non-profit corporate entity to promote OpenStack and its community.
There is supersonic speed and agility in the cloud. 1000s of servers can be built in minutes. Archive, backup, file storage, content distribution services, email services, iOT, hybrid helps be in on-premises or on Cloud. There are 3500 products from 1100 sellers on Cloud these days.
There is 300 million hours of usage of the software.
112% growth year on year of Cloud users. Also everyday there are 3 new capabilities added to cloud computing.
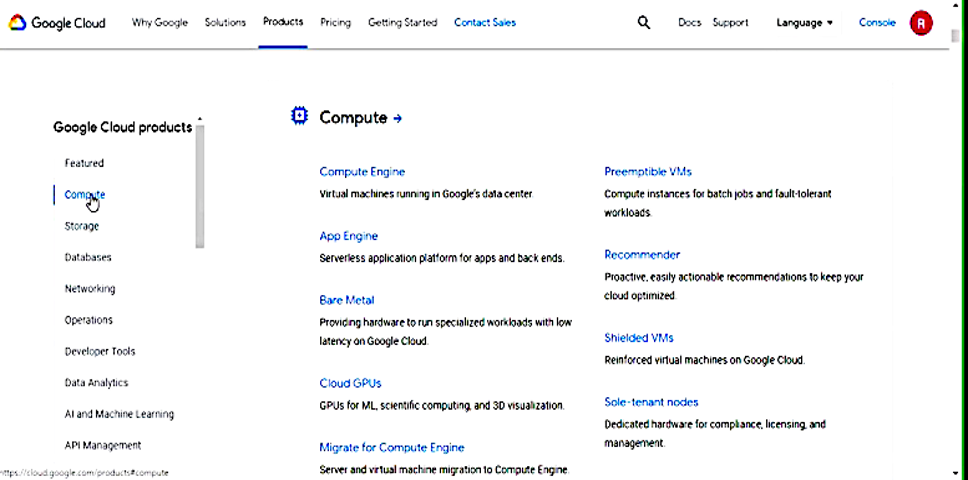
- 1.1. Cloud services in IT infrastructure and use of Cloud infrastructure
We can use Infrastructure as a Service (IaaS) model for e-commerce as it promises higher security than other models.
IaaS provides cloud-based services which provide pay-as-you-go for services such as storage, networking, and virtualisation.
For securing data communication for highly confidential data for any enterprise, the most suitable architecture is IaaS.
Infrastructure as a Service (IaaS) includes:
Virtualisation, storage, servers and networking.
We can use AWS CloudFormation to plan, deploy, deploy the cloud infrastructure.
There’s more computing power than IaaS, as it’s a virtual machine.
IaaS has a market share of 12% (increase from 6%).
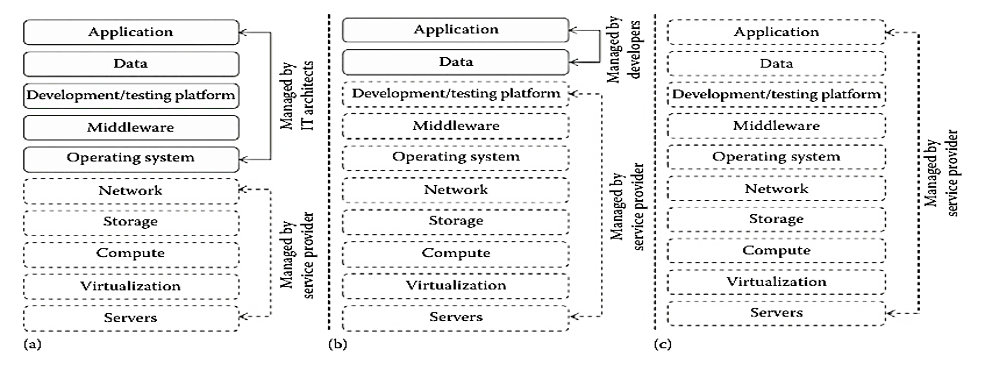
In IaaS application, data, development or testing platform, middleware and operating system is managed by the IT architects. Whereas, network, storage, computing, virtualisation and server is managed by the service provider.
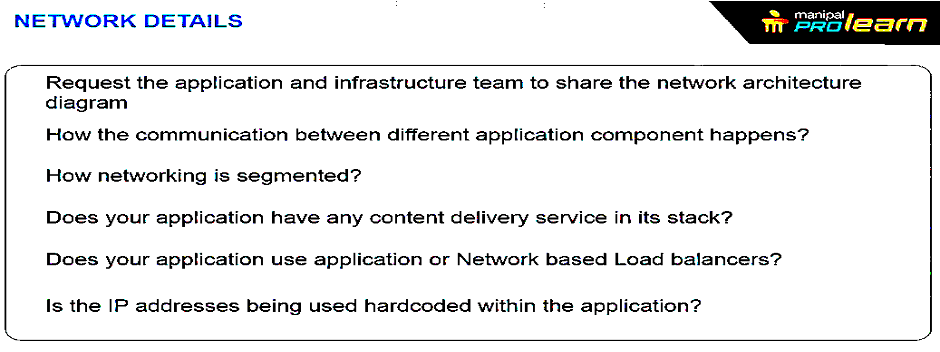
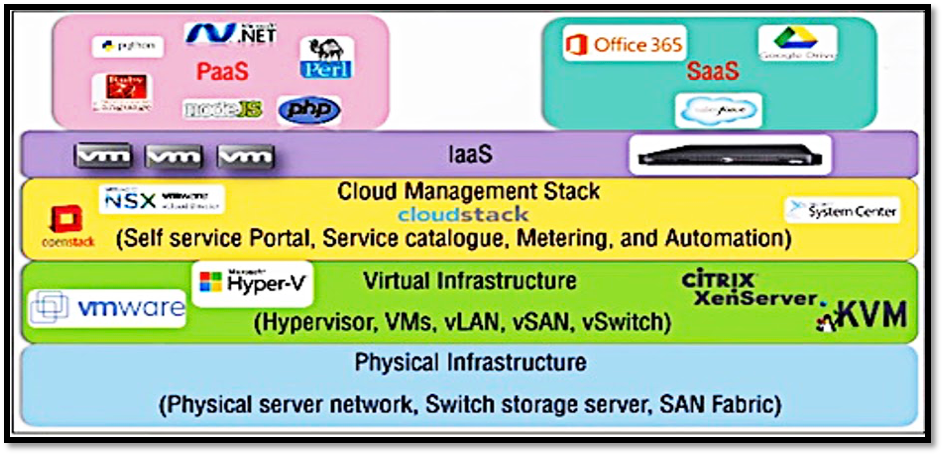
The architecture of cloud infrastructure:
It consists of physical infrastructure, virtual infrastructure, cloud management stack.
On top of physical infrastructure we have virtual infrastructure.
On top of virtual infrastructure we have a cloud management stack. And on the top of it we have infrastructure as a service (IaaS).
On top of Infrastructure as a Service we have Software as a Service and Platform as a Service.
The physical infrastructure includes a physical server network, switch storage server and SAN Fabric.
The virtual infrastructure contains hypervisor, VMs, vLAN, vSAN and vSwitch.
The cloud management stack contains self-service portal, Service catalogue, metering and automation.
Cloud force, Microsoft 365, Google Drive examples of Software as a Service.
PHP, .net, Python, Ruby, Perl, node.js come under Platform as a Service.
Benefits of Cloud computing
Properties of cloud computing:
- Scalability: It has dynamic provision and multi-tenant design.
- Availability/reliability: It is Fault tolerance with system security and system resilience.
- Manageability/interoperability: It helps in control automation, system monitoring and billing systems.
- Accessibility/portability: It can be used on any equipment.
- Performance optimisation: Job scheduling, load balancing, parallel computing.
- Job scheduling: If the printer comes under services, all the users request the printer to print the same document at same time. It enables you to check which user requested first.
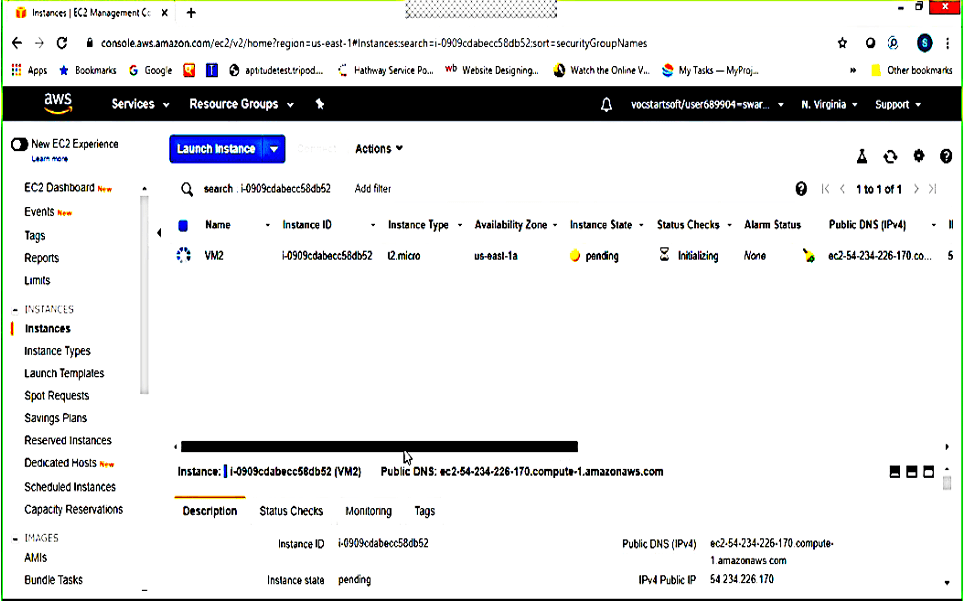
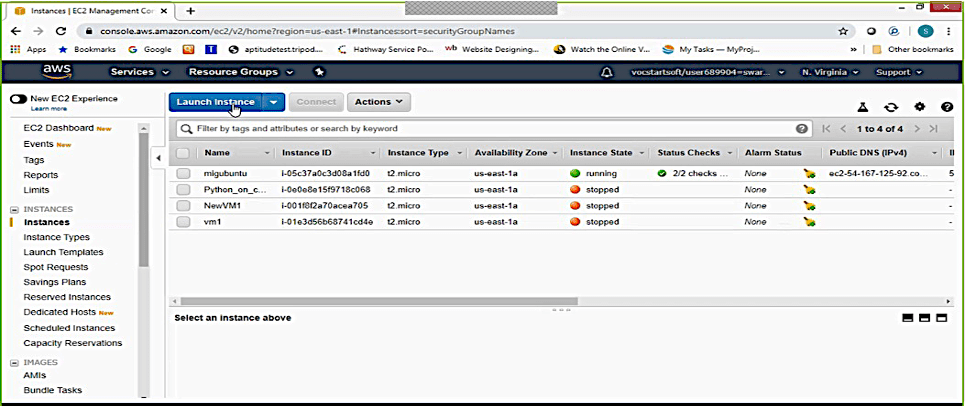
Amazon elastic cloud compute (Amazon EC2) is a web service that provides re-sizeable computing power. It lost to configure and obtain capacity with minimal friction. It provides the user with complete control on the computing power with least friction. It allows us to boost and obtain new server instances in minutes allowing us to quickly scale capacity. It allows users to pay for only the capacity they use.
Cloud computing in e-commerce
Figure 1.5a: Traditional E-commerce industry chain
Capabilities of cloud computing
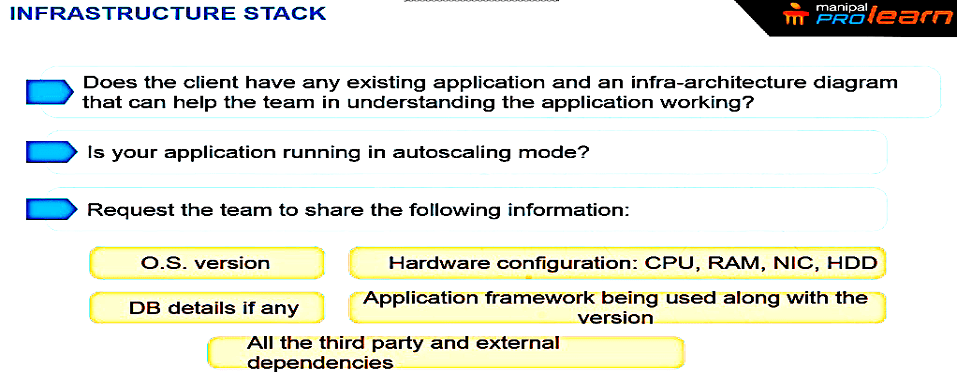
Infrastructure is considered the backbone of the Cloud. It determines the Quality of Service factor.
For setting up an infrastructure the team needs to tell:
Operating system version
If there is any database involved its detail
Third-party dependencies
Hard work configuration like CPU, RAM, NIC and HDD.
If the application is working on auto scaling mode it can balance if there is a lot of traffic on the application/website or there is very less traffic.
Controlled interface
The integrated infrastructure is responsive to change. The demand of the platform owner in managing or controlling it’s also a capability. Apple iPhone makes money from application purchase on top. Microsoft earns money from selling the product license.
It is independent of location
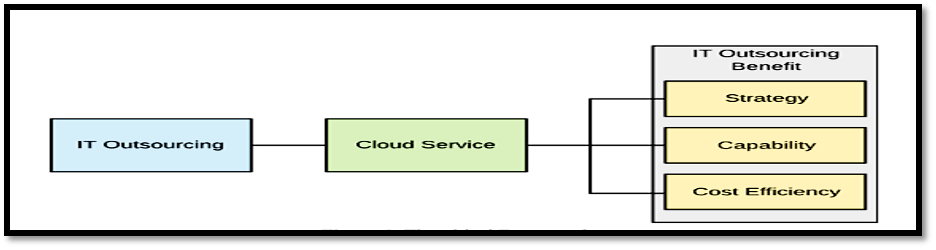
1. Strategy for cloud computing
Cloud strategy is a plan of action to layout the different ways to use cloud resources. Cloud strategy is to anticipate the market and then plan accordingly to move forward. It enables the website to differentiate, change and to gain an edge in the industry. Cloud is an inexpensive and practical technology for problem solving. In today’s rapidly growing era, cloud is the best option for cost-effective data storage.90% of the business organisations are focusing on the first cloud strategies for the advancement of cloud computing services.
Strategic planning is very important to analyse the service, business needs and requirements of the business before investing in a huge amount for cloud computing. It is very important to keep a few aspects in mind like:
- Client accessing facility
- Data backup requirement
- Budget requirement
- Type of deployment models of cloud:
- private,
- public,
- community or
- hybrid.
- Privacy and Data security
- Data backup requirement
- Data export requirement
- Requirement of training
It is very important to keep the above-mentioned aspects in mind and to choose the best cloud host accordingly. The value proposition of the cloud is considered here, in this it is important to gain information about things like the high quality of service outsourcing, low-cost, maintenance cost reduction, innovation etc. The strategy of cloud technology is analysed on this basis. Strategy planning is always done for profit maximisation of the company.
The factors that need to be considered before investing in cloud technology are:
- Availability
- Compliance
- Compatibility
- Monitoring
1.1. Develop a cloud-first and multi-cloud strategy
The cloud-first strategy enables a website to save money on software, infrastructure and platforms. In this the business aims to utilise the most of the services provided. Considering cloud computing is the foremost thing to do by a business once it opens. Prioritising cloud computing investments will give an upper hand to the company’s business in the market. As cloud is very inexpensive it will not take much investment and in return will provide amazing data storing services with security which will save some capital in the e-commerce company to invest on other important aspects.
1.2. Continuously practice workload placement analysis
Proper management of the data available as well as its accessibility is very important. Continuous workload placement analysis includes to analyse and re-analyse the workloads at a regular basis so to be updated as if the current placement of data is fulfilling the requirement of the company or not. Hence cloud computing provides services which make the process easy to be updated on the data storage, cloud is accessible to a person from any part of the world. Its scalable feature enables the host to align with the requirements of the company within a short notice, hence eliminating the issue of downtime.
1.3. Develop a multi-cloud management tooling strategy
1.4. Benefits of the strategies:
1.4.1. Improved IT security
The main concern for any company for moving the database to virtual is of security. Cloud technology provides a different deployment model which enables the user to choose the service and the population it needs to be accessed by, the access to the specific database then have different barriers to ensure the safety of the database.
1.4.2. Reduce time-to-market
To have a constant customer base it is important to have fast and quality service. Cloud technology enables websites to entertain any amount of customers on the site.
1.4.3. Increase competitiveness and margins
Cloud technology helps to save money on renting a place, owning the hardware, housing, staffing and maintenance. The capital saved can be used in other areas to increase profits.
1.4.4. Competitive advantage
Faster, safer and an intelligent technique and its proper usage will ramp up the performance of the company in the market by increasing its productivity.
2. Cost effectiveness in cloud computing
3. Analysis of companies
4. Security in E-Commerce: Issues and Attacks
4.1. Data Security
Traditionally all the applications are developed in the premises of the enterprise, because of limited boundary access of application it’s easy to form software secure physically, logically, providing personal security to the software and securing application data by the access control policies.
However, data resides in SaaS model the limited boundary crosses the enterprise and enterprise data is share outside the enterprise boundary, which is at the SaaS vendor. Now the SaaS vendor provides security of knowledge . Because of multiple user vendor must adopt the extra security checks for make sure the data security and stop unauthorised data access due to security vulnerabilities. For securing data strong encryption techniques are used and different authorized access control mechanisms are implemented.
For security check at the SaaS vendor the subsequent assessments tests are used:
- Hidden field manipulation
- Insecure storage
- Cookie manipulation
- Cross site scripting
- Access control weakness
- Insecure configuration
- Cross site request forgery
- OS and SQL injection clause
During test if any vulnerability detected this test are often avoid access to sensitive enterprise data and which causes a financial lost to enterprise.
4.2. Network Security
In cloud, the robust network association could also be a backbone of the cloud infrastructure. Whenever enterprise employing a SaaS development model the process sensitive information is obtained from enterprise processed by the SaaS application and stored at the SaaS marketer finish. For this, information flow network is needed. For preventing leak of sensitive information network should be extremely secured. For Security, network robust network traffic secret writing techniques square measure used like Secured Socket Layer (SSL) and Transport Layer Security(TLS).
In no matter extends,
Network penetration And packet analysis
Insecure SSL trust configuration
Session management weaknesses
4.3. Data Integrity
For storage of knowledge, information systems square measure used. In standalone system knowledge integrity is well maintained; because of single information. In standalone information, system manages knowledge integrity through information constraints and transactions. All the information transactions ought to need to follow the ACID (atomicity, consistency, isolation and durability) that ensures the info integrity.
In cloud distributed systems square measure used, multiple databases are settled on varied locations rather than same location along with multiple applications square measure along used for knowledge storage. attributable to distributed information, multiple users will simultaneously access the info and multiple transactions square measure simultaneously performed. attributable to multiple transactions over multiple knowledge sources it’s ought to be handle properly without misplaced the any single little bit of data; central world transaction manager will this. For integrate the info in distributed network every application ought to be able to participate in world dealings via a resource manager. This can be achieved victimisation two-phase commit protocol.
4.4. Authentication and Authorisation
In little and medium business organisations, Light
Weight Direction Access protocol (LDAP) or Active Directional theme used for maintaining worker information. whereas most of the organisations currently adapt to the SaaS, they presumably to use AD theme tool for managing users. currently by victimisation SaaS all worker information shared outside the corporate setting. SaaS providers solely provides the service they’re obsessed with the SaaS client for take away / disable accounts as per employee leave the organisation & produce / change accounts as per new connection.
4.5. Data Access
Each user has totally different rights in organisation for knowledge access. knowledge access is especially specialise in those security policies provided to the user for knowledge access. In ancient systems, little business organisation sets their own security policies for the set of information that worker will have. These access policies to access the information sets area unit set by organisations. There unauthorised users ought to replicate security policies in cloud to avoid intrusion of information.
Cloud suppliers ought to limit structure knowledge boundary for distinguish between multiple structure knowledge. To handle the protection policies forwarded by the structure the cloud SaaS model ought to be versatile.
During these check if any vulnerability detected, test can be exploited to hijack active session, gain access to user credentials and sensitive information.
Cloud Computing Attacks
Distributed DoS
Many users sheared a standard medium of knowledge access in cloud infrastructure, thanks to an equivalent cloud is additional susceptible to DoS attacks. The common sharing medium makes DoS attacks far more damaging. Whenever high employment is noticed on the flooded service, Cloud computing package starts to produce additional process power to address the extra work load. By providing additional process power cloud system making an attempt to figure against the wrongdoer until the server hardware boundaries however really to some extends even supports wrongdoer by facultative them to try to to most doable harm.
Cloud Malware Injection Attack
Cloud Malware Injection Attack aims to inject a malicious service, application or virtual machine in between licensed communication medium tries to break the cloud infrastructure. Once aggressor succeeds enter malicious package in cloud structure as he cares for the malicious package as legitimate request. If licensed user asks for malicious package that is shown as legitimate, by accessing those package virus enters in cloud infrastructure and tries to damage user connected data. Whenever user offers request for this malicious package uploaded virus is unfold throw web and tries to infect additional and additional files by replicating itself or by external attachment. Finally infection flooded in to the cloud structure and cloud infrastructure could majorly damages if infection is goodbye unobserved.
Authentication Attack
Most frequently targeted a part of cloud is Authentication that is weakest in hosted and virtual service. ways and mechanisms used for secure the authentication are oftentimes targeted by the offender. As per fine arts configuration of cloud infrastructure cloud offer forms of service models SaaS, PaaS and IaaS out of these 3 solely IaaS giving these varieties of info protection and encoding. For securing digital communication, best suited design is IaaS for extremely confidential information for any enterprise. additionally, the user facet (enterprises) to rather than the service suppliers for those information belonged to the enterprises however keep on the service provider’s facet should authorize the authorization of knowledge method or management. varied kinds of secondary authentication (such as website keys, virtual keyboards, shared secret queries, etc.) are employed by some money establishments to shield the system by tougher for fashionable phishing attacks however still a number of them uses easy most user-facing services that is username and parole style of knowledge-based authentication.